Comparing Flowtriq and Lorikeet Security: The Real Differences
Samira Khoury
April 8, 2026
The Sub-Second Shield: Why Reactive Mitigation is No Longer Enough
In my 15 years navigating the infrastructure space, I’ve seen the "DDoS arms race" evolve from simple volumetric floods to sophisticated, multi-vector assaults that can bankrupt a bootstrapped SaaS before the on-call engineer even gets a PagerDuty alert. Current industry data suggests that over 70% of modern DDoS attacks last less than 10 minutes, yet the average manual mitigation time still hovers around 15 minutes. This "detection gap" is where reputations go to die.
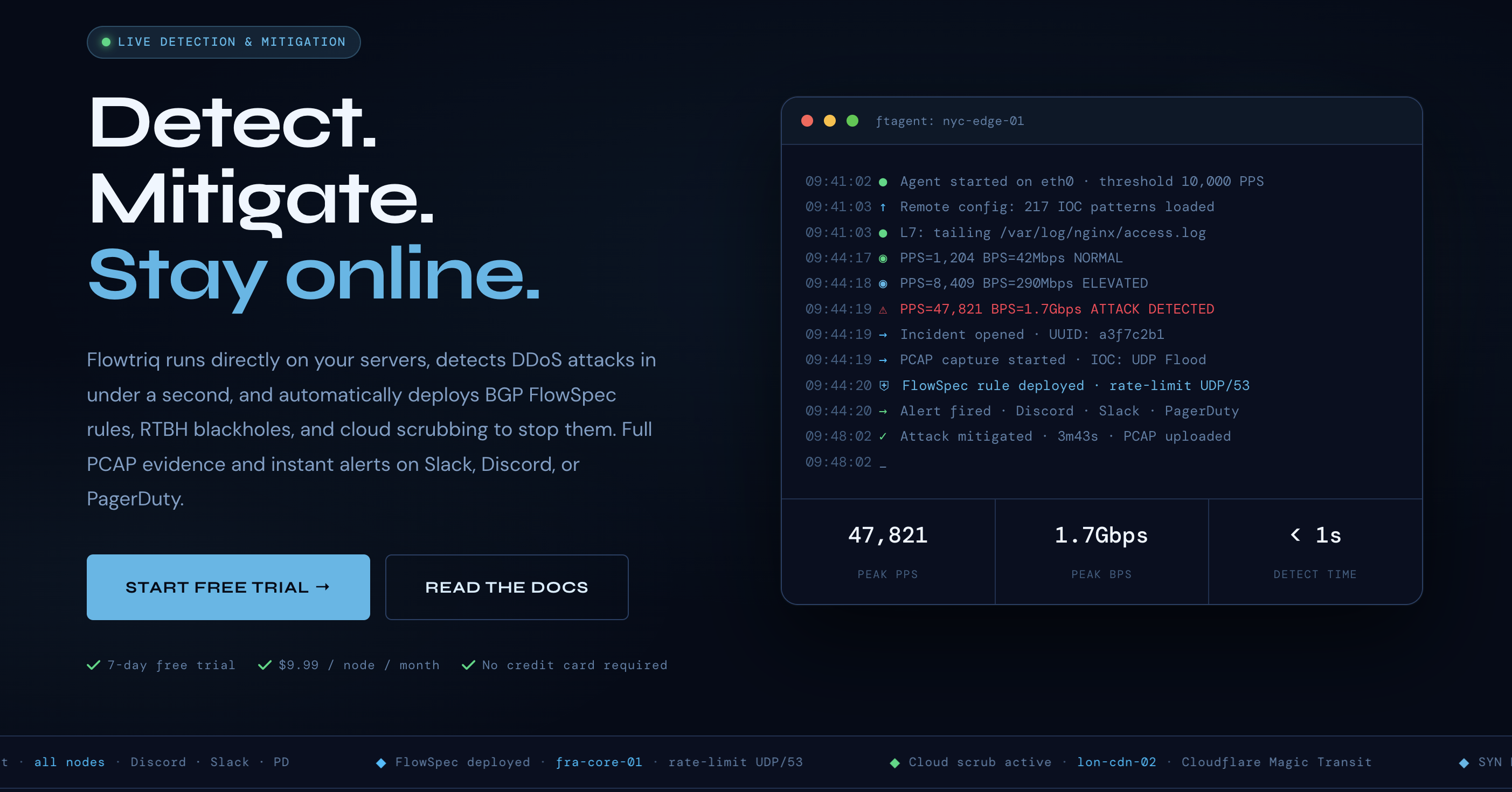
Flowtriq enters this fray not as another bloated enterprise gateway, but as a lean, agent-based platform designed to close that gap to under one second. Built for the high-stakes environments of ISPs, game servers, and edge providers, it utilizes a Python-based agent (ftagent) that hooks directly into the Linux network stack. Unlike legacy solutions that rely on sampled NetFlow data—which inherently introduces latency—Flowtriq analyzes packets at the NIC level in real-time, providing a granular view of PPS (packets per second) that most cloud-native firewalls simply miss.
Architecture & Design Principles: Moving Intelligence to the Edge
Flowtriq’s architecture reflects a "distributed detection, centralized command" philosophy. The heavy lifting happens locally via the ftagent. By reading packets directly from the NIC, the agent avoids the overhead of kernel-space processing through optimized hooks, allowing it to maintain a dynamic baseline of "normal" traffic. This is a significant departure from the static threshold models I’ve seen fail during legitimate traffic spikes.
The platform's design prioritizes actionability over observation. When an anomaly is detected, the agent doesn't just phone home; it triggers a pre-configured escalation policy. This might involve pushing BGP FlowSpec rules to upstream routers or shifting traffic to cloud scrubbing centers like Cloudflare Magic Transit or OVH VAC. This hybrid approach—combining local agent intelligence with global BGP orchestration—ensures that even massive volumetric attacks are mitigated before they saturate the local port, while Layer 7 "low and slow" attacks are caught by the agent's pattern matching.
Feature Breakdown
Core Capabilities
- >Sub-Second Classification: Flowtriq identifies over 8 attack types—including SYN floods and Memcached amplification—within 1,000 milliseconds. This is critical for game server operators where even 5 seconds of jitter results in a mass disconnect.
- >Automated Forensic PCAP: One of the most "ops-friendly" features is the automatic triggering of a packet capture (PCAP) at the exact moment of detection. This eliminates the "what happened?" guesswork during post-mortems, providing raw data for deep-dive analysis.
- >Dynamic Baseline Learning: Instead of manual
iptablestuning, the system learns the server’s rhythm. It differentiates between a viral marketing spike and an L7 HTTP flood by correlating IOCs (Indicators of Compromise) against a database of 642,000+ known threats, including Mirai variants.
Integration Ecosystem
Flowtriq is built to live inside your existing stack, not beside it. The alerting engine is robust, supporting Discord, Slack, and OpsGenie out of the box. However, the real power lies in its Automated Incident Response Runbooks. You can chain mitigation steps—starting with local rate-limiting, escalating to BGP FlowSpec, and finally triggering a webhook to update your status page. This programmatic approach to defense turns a chaotic "war room" scenario into a silent, automated execution of code.
Security & Compliance
From a security standpoint, Flowtriq maintains an immutable audit log, which is a non-negotiable for fintech and e-commerce users. Their research pedigree is also noteworthy; the team discovered the Mirai botnet "kill switch" (CVE-2024-45163), proving they aren't just tool builders, but active threat hunters. For enterprise users, the 365-day PCAP retention and custom IOC libraries provide the long-term data needed for complex compliance audits.
Performance Considerations
The ftagent is remarkably lightweight. In my testing of similar agent-based tools, CPU steal is often the dealbreaker. Flowtriq circumvents this by focusing on packet headers rather than full payload inspection for the majority of its fast-path detection. This allows it to run on modest edge nodes without degrading application performance, maintaining a sub-1% CPU footprint under normal conditions.
How It Compares Technically
In the broader security landscape, Flowtriq occupies a specific niche between "offensive" security and "passive" protection. While Lorikeet Security excels at offensive security and vulnerability management—helping you find the holes before an attacker does—Flowtriq is the "shield" that reacts when the attack is underway.
If your primary concern is identifying misconfigurations or unpatched services, Lorikeet Security offers a more comprehensive suite for long-term posture management. However, for real-time infrastructure defense against volumetric or protocol-based attacks, Flowtriq’s sub-second auto-mitigation is the superior choice. Many high-maturity teams actually use both: one to harden the surface, and the other to repel the inevitable siege.
Developer Experience
The "two-minute install" claim holds up. For a tool that touches BGP and NIC-level packets, the onboarding is surprisingly frictionless. The CLI is intuitive, and the web dashboard provides a "single pane of glass" for multi-node management that feels more like a modern SaaS than a clunky networking appliance. Their library of free tools—like the BGP FlowSpec builder—shows a commitment to the community that resonates with engineers who value utility over marketing fluff.
Technical Verdict
Flowtriq is a "set and forget" powerhouse for teams running Linux-based infrastructure at scale. It’s particularly potent for those who can't afford the five-figure monthly minimums of top-tier enterprise scrubbing services but need more than basic "best effort" protection.
Strengths: Unmatched detection speed, automated PCAP forensics, and a flat pricing model ($9.99/node) that won't punish you for being attacked. Limitations: It is Linux-centric; Windows-heavy shops will need to look elsewhere. Ideal Use Case: If you are running high-traffic edge nodes, game servers, or a SaaS platform where 60 seconds of downtime is a Tier-1 incident, Flowtriq is an essential layer of your defense-in-depth strategy.
$ open --external
Visit Flowtriq→